 |
| Source@goup-ib |
A new APT group, known as Dark Pink, has been discovered by cybersecurity firm Group-IB. The group, which has been active since mid-2021, has been found to be targeting military branches, government ministries, and agencies in the APAC region, as well as one organization in Europe. As of December 2022, Dark Pink had successfully breached the defenses of six organizations in five APAC countries (Cambodia, Indonesia, Malaysia, Philippines, and Vietnam), and one organization in Europe (Bosnia and Herzegovina).
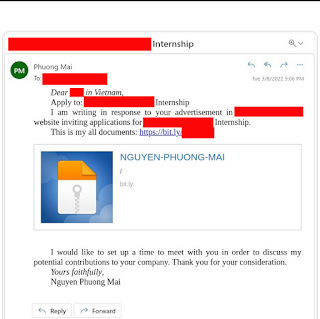
Dark Pink uses a variety of custom tools and sophisticated tactics, techniques, and procedures (TTPs) to launch its attacks. The group begins with targeted spear-phishing emails, using a shortened URL to direct victims to a file sharing site where they can download a malicious ISO file. This file contains three different file types: a signed executable file, a non-malicious decoy document, and a malicious DLL file. However, the contents and functionality of these files can vary, with Group-IB analysts discovering three separate kill chains used by the group.
The first kill chain sees the threat actors pack all the files, including a malicious DLL, onto the ISO itself. After the ISO is mounted, the DLL will be run using the attack known as DLL Side-Loading. The second kill chain sees the threat actors leverage Github after initial access, allowing them to download additional malicious files. The third kill chain involves the use of a malicious DLL file that is launched using the DLL Hijacking technique.
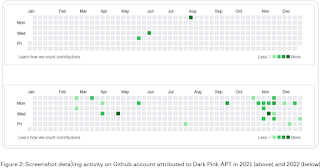
Group-IB's Threat Intelligence Team also discovered that the group uses the same Github account to upload malicious files throughout the entire duration of the APT campaign, which suggests that the group has been able to operate without detection for a significant period of time. The group has also been found to scan job boards and craft unique phishing emails relevant to the organization they are targeting.
The Dark Pink APT group is notable for its specific focus on attacking military branches, government ministries, and agencies. Group-IB has been unable to attribute the group's campaign to any known threat actor and believes that it is the activity of an entirely new group, which has also been termed Saaiwc Group by Chinese cybersecurity researchers. With their custom tools and sophisticated tactics, the Dark Pink APT group poses a significant threat to organizations in the APAC region and Europe.




No comments:
Post a Comment